UPDATE – Script now will convert CR to LF line endings for better reliability with old PPDs
There are some good hints for adding printers via the command line with lpadmin: Managing multiple printers via the command line
However, there is still confusion surrounding the setting of printer options from the command line, as a poster to Debian bugs pointed out back in 2006: lpoptions documentation doesn’t. After doing some testing, here’s the two main takewaways:
- If you use lpadmin and specify options with “-o” the PPD is altered and OS X will recognize the options for the printer.
- However, if you setup the printer using lpadmin without any options and later use lptoptions to set the options, they are not written to the PPD and the GUI is unaware of the printer’s options.
more helpful hints about lpadmin and lpoptions:
lpoptions -p printername -l
- Prints PPD options, “Default” is filtered out from option name (compared to looking at the raw PPD)
- It uses a colon when reporting key value pairs, however replace that with an equals sign when specifying an option
- The option name stops at the first slash
- Example: The duplex option for HP printers will output like this “HPOption_Duplexer/Duplex Unit: *True False”
When specified as a “-o” option it would be “HPOption_Duplexer=True”lpadmin … -o this=that
- Alters the ppd that is placed in /etc/cups/ppd/ when the printer is installed
Unhelpful things:
lpoptions -p printername
- These are NOT the PPD options you want to set
lpoptions -o
- Only writes options to: /private/etc/cups/lpoptions (run with sudo) or ~/.cups/lpoptions (run as current user), GUI apps are unaware of these options
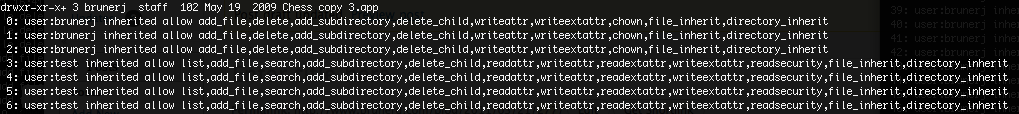
The following script compares the original and the newly installed PPD to generate the options syntax to be used with lpadmin:
The main magic in this script is a little diff and sed:
diff "$originalfile" "$newfile" | grep "> [*]Default" | sed 's/> [*]Default/-o /g' | sed 's/: /=/g'
Script Workflow
- Copy and paste the script into TextWrangler (or download ppdOptionsDiff.command), save with a .command extension and it will automatically take care of the executable bit
- Setup your printer via the Printers Preference Pane in the GUI.
- Look in /etc/cups/ppd and find the newest .ppd (it will be named as the printer)
- Locate the original .ppd.gz (or .ppd) in /Library/Printers/PPDs/Contents/Resources/, usually the printer ppd is easily found by name, but some like Canon have some cryptic filenames, so look inside the /etc/cup/ppd file, the “PCFileName” variable sometimes helps to determine the file name
- Run the script given below, it will ask you to drag in the original and the modified ppds. Out will come the “-o” options for use with lpadmin
You can also run the script with the original and modified file paths as arguments and the string will be output
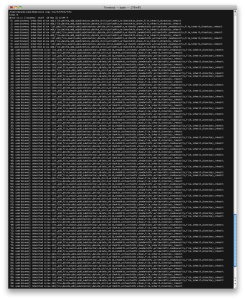
The script “ppdOptionsDiff.command“:
#!/bin/bash
[ -f /tmp/debug ] && set -x
#ppd option maker
#help
if [ "$1" == "-h" ]; then
echo "$(basename $0) compares two ppds and outputs the differences as a string for use in lpadmin"
echo "Usage: $(basename $0) [original_ppd] [new_ppd]"
exit
fi
#check for parameter if not ask
if [ -z "$1" -o -z "$2" ]; then
clear;
echo "Drag in the unmodified PPD from /Library/Printers/PPDs/Contents/Resources:"
open /Library/Printers/PPDs/Contents/Resources
while [ -z "$originalfile" ]; do
read originalfile
done
echo "Drag in the PPD from /etc/cups/ppd:"
open /etc/cups/ppd
while [ -z "$newfile" ]; do
read newfile
done
#else just take the arguments
elif [ -n "$1" -o -n "$2" ]; then
newfile="$2"
originalfile="$1"
fi
#make a temp file of the original to compare
#strip off path and extension for temp file name
tempOriginalFile="/tmp/$(basename "$originalfile" .gz)"
#if file is compressed expand
if [ "${originalfile##*.}" == "gz" ]; then
#uncompress
IFS=$'\n\t'
#gunzip to temp file
gunzip < "$originalfile" > "$tempOriginalFile"
else
#just make a copy
cp "$originalfile" "$tempOriginalFile"
fi
#change line endings from CR to LF (diff fails unless this is done)
sed -e $'s/\\\r/\\\n/g' -i '' "$tempOriginalFile"
#make a temp file of the new file to compare
#strip off path
tempNewFile="/tmp/$(basename "$newfile")"
cp "$newfile" "$tempNewFile"
#change line endings from CR to LF (diff fails unless this is done)
sed -e $'s/\\\r/\\\n/g' -i '' "$tempNewFile"
#test for file existence
if [ ! -f "$tempOriginalFile" ]; then echo "$tempOriginalFile is not a valid path"; exit; fi
if [ ! -f "$tempNewFile" ]; then echo "$tempNewFile is not a valid path"; exit; fi
#create options list by diffing and filtering
optionList=$(diff "$tempOriginalFile" "$tempNewFile" | grep "> [*]Default" | sed 's/> [*]Default/-o /g' | sed 's/: /=/g')
#print out the options with no line breaks
IFS=$'\n\t'
if [ ! -z "$optionList" ]; then
for option in $optionList; do
echo -n "$option "
done
echo
else
echo "No differences"
fi
#delete the temp filess
rm "$tempOriginalFile" "$tempNewFile"
exitExample (with pathnames provided as arguments, otherwise runs in interactive mode):
$ ./ppdOptionsDiff.command /Library/Printers/PPDs/Contents/Resources/HP\ LaserJet\ 5200.gz /private/etc/cups/ppd/PRINTERNAME.ppd
-o HPOption_Tray3=Tray3_500 -o HPCollateSupported=True -o HPOption_Duplexer=True -o HPOption_Disk=RAMDisk
Use the generated string in lpadmin to set the printer options, like this example:
lpadmin -p "Ye_Olde_LaserJet" -D "Ye Olde LaserJet" -E -v socket://x.x.x.x -P /Library/Printers/PPDs/Contents/Resources/HP\ LaserJet\ 5200.gz -L "Location is in a closet in a sub-basement, good luck" -D -o HPOption_Tray3=Tray3_500 -o HPCollateSupported=True -o HPOption_Duplexer=True -o HPOption_Disk=RAMDisk -o printer-is-shared=falseThe documentation from man lpadmin is a bit obtuse and lacking. For example: -E will enable the printer (essential!) except when used before -p or -d in those cases it forces encryption, so watch out! Also, in the man page it shows -h server[:port] but -h is not documented anywhere in there and I have never used it. Rather, the -v option should be used with a URL like lpd://, socket:// (HP), ipp://, etc.. if you want to get a listing of the protocols run lpinfo -v this will even do a look around with Bonjour to see what’s on the network (they are dnssd://). The -p option is the CUPS queue name, it does not allow spaces, whereas the -D option is the “friendly name” that a user will see in macOS, you can set some location text with -L and finally just tack all the -o options on the end. -o printer-is-shared=false will keep the printer from being broadcast if you turn on Printer Sharing (or if a user accidentally turns it on)