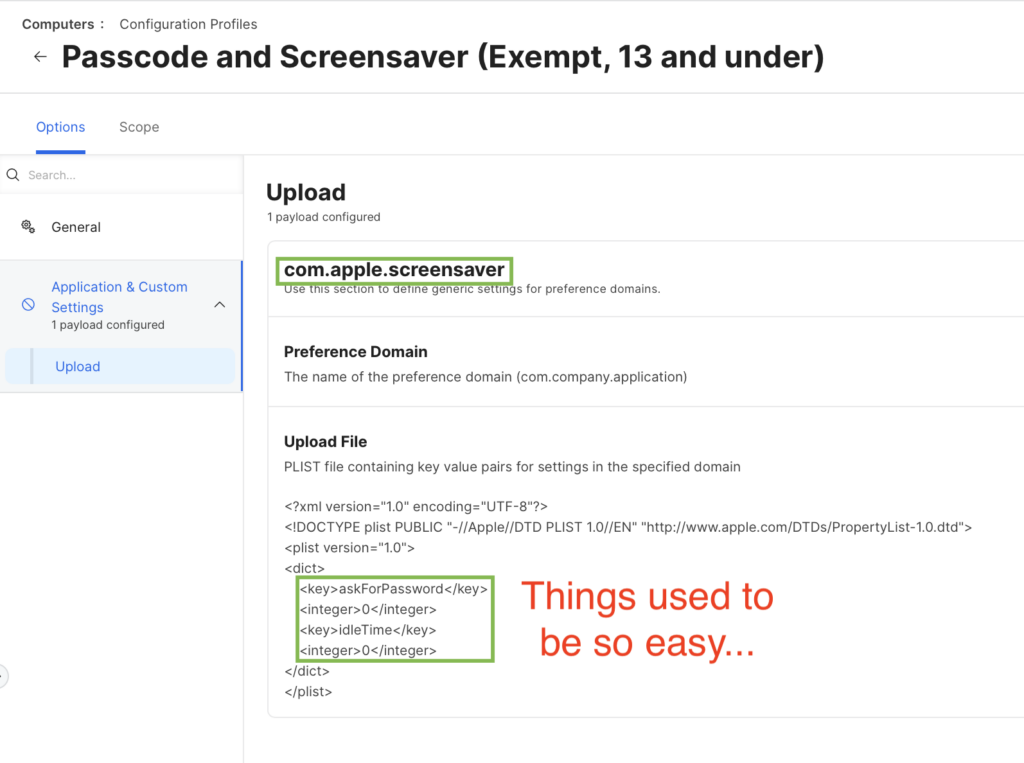
So here’s the situation: You have a Mac mini that’s used as a Zoom Room controller. You’ve enabled automatic login. You don’t want the screensaver to come on ever and it should never ask for a password if the screen is turned off. This is a common ask and used to be really simple. You’d just go into Jamf, create a configuration profile, add the Applications & Custom Settings payload, choose Upload, set the domain to com.apple.screensaver and add two XML keys askForPassword and idleTime set to integer 0. This is known as an “MCX” style payload, they are from the olden OS X Server days.
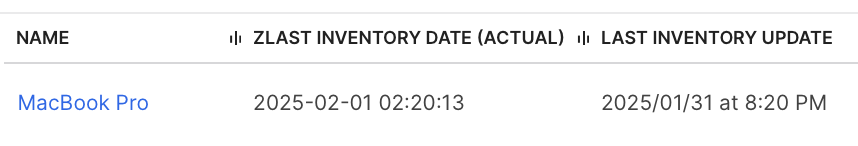
You made this payload years ago and it worked reliably for years. Until Sonoma came out. Then you were hearing that Zoom Rooms were restarting after OS updates to the “lock screen” requiring a password?! What was going on? You open a Feedback and ACE case, you are asked for sysdiagnoses even though they are attached and you hear nothing. The summer passes, Sequoia comes out, “darn seems like they didn’t fix this”, you think. Then you wonder, maybe it’s not the OS that’s broken but something else?
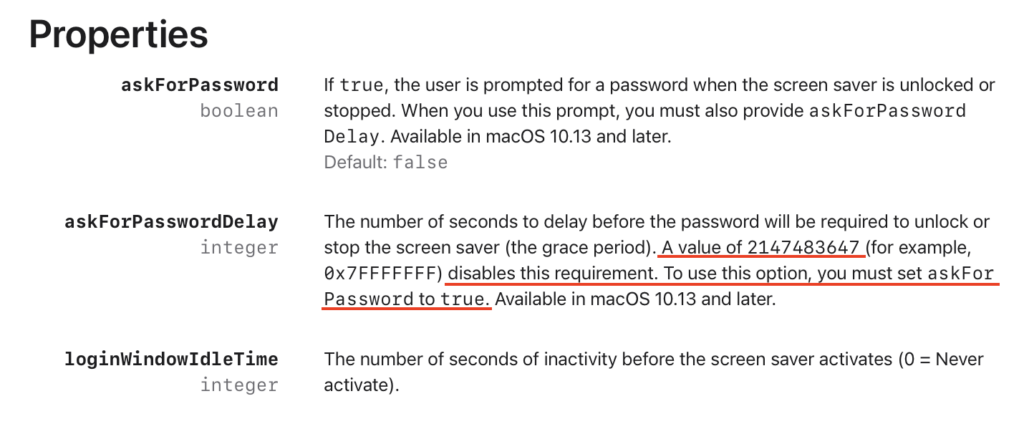
Turns out Apple changed how macOS it interprets the Screensaver domain keys in an MCX style payload. Apparently, it can’t tolerate them any more. Integer values of 0 now cause it to Immediately ask for password! Now, instead of setting askForPassword to the integer 0 it’s boolean and you need to set that to true (yeah, that’s right, true) and then you set the key askForPasswordDelay to… yeah, you got it: 2147483647! That’s what you were gonna say right? 😑 See the Apple documentation and check your incredulity at the door, they say this has been around since 10.11 and the crazy high askForPasswordDelay value they say came about in 10.13 but macOS sure as heck respected the simple MCX style payloads up until macOS 13!? So is this a typo? Regardless it’s super unintuitive, unfriendly and non-obvious
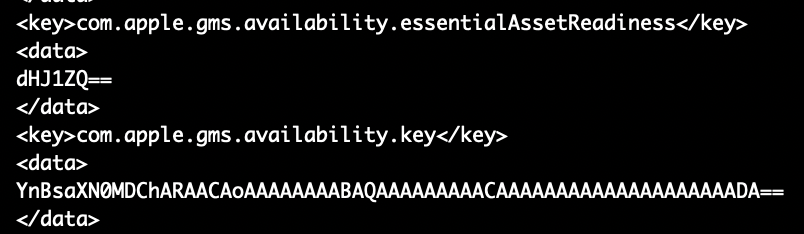
Thankfully, they didn’t mess with how idleTime is interpreted, it still works as an integer set to 0. Here’s the whole thing in an MDM .mobileconfig file.
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<key>PayloadContent</key>
<array>
<dict>
<key>PayloadDisplayName</key>
<string>Screensaver</string>
<key>PayloadIdentifier</key>
<string>com.apple.screensaver.9ABFE38F-2822-47FD-B2E3-5FBC49AFAD1B</string>
<key>PayloadType</key>
<string>com.apple.screensaver</string>
<key>PayloadUUID</key>
<string>9ABFE38F-2822-47FD-B2E3-5FBC49AFAD1B</string>
<key>PayloadVersion</key>
<integer>1</integer>
<key>askForPassword</key>
<true/>
<key>askForPasswordDelay</key>
<integer>2147483647</integer>
<key>idleTime</key>
<integer>0</integer>
<key>loginWindowIdleTime</key>
<integer>0</integer>
</dict>
</array>
<key>PayloadDescription</key>
<string>Disallows screensaver and lock screen password</string>
<key>PayloadDisplayName</key>
<string>Passcode and Screensaver (Exempt, 14 up)</string>
<key>PayloadIdentifier</key>
<string>com.example.zoomroom.screensaver-passcode</string>
<key>PayloadType</key>
<string>Configuration</string>
<key>PayloadUUID</key>
<string>FBD0991C-8F71-4F69-98D9-4F03943C420A</string>
<key>PayloadVersion</key>
<integer>1</integer>
</dict>
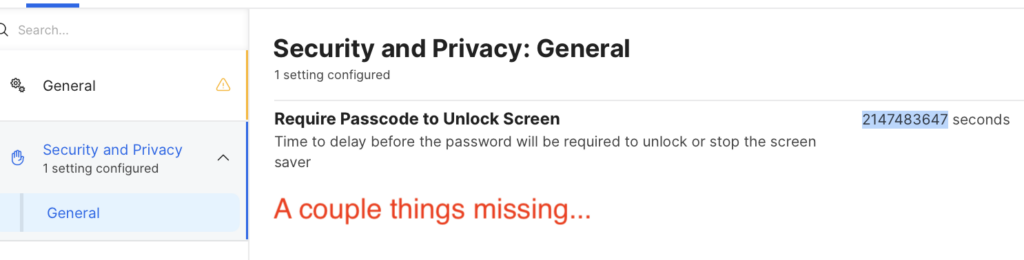
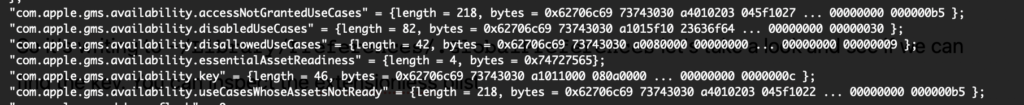
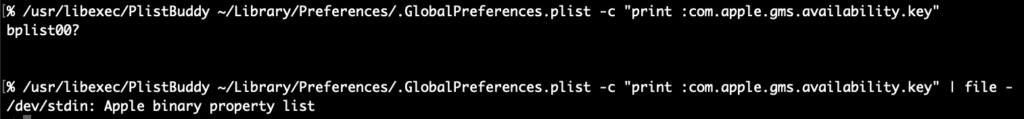
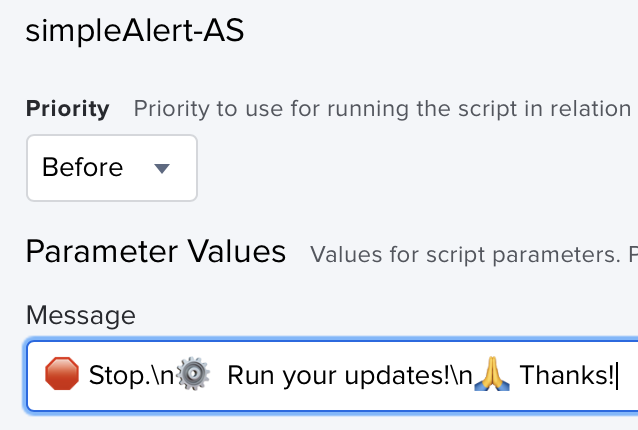
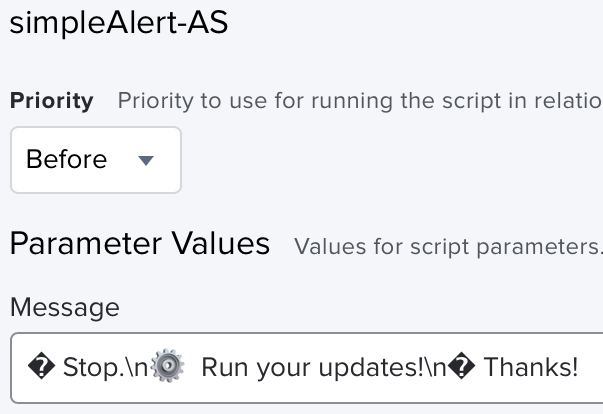
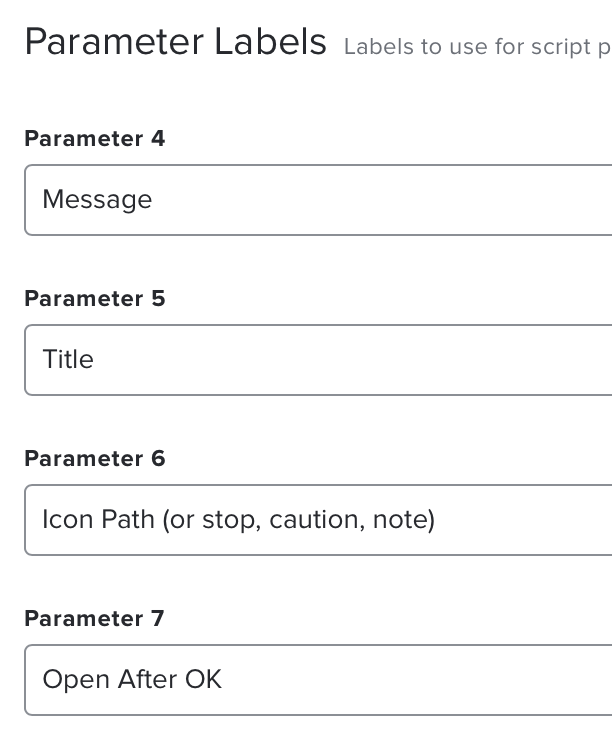
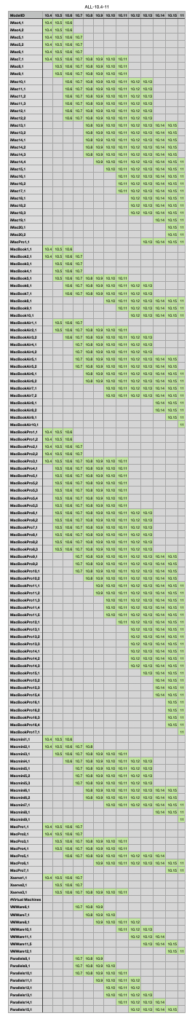
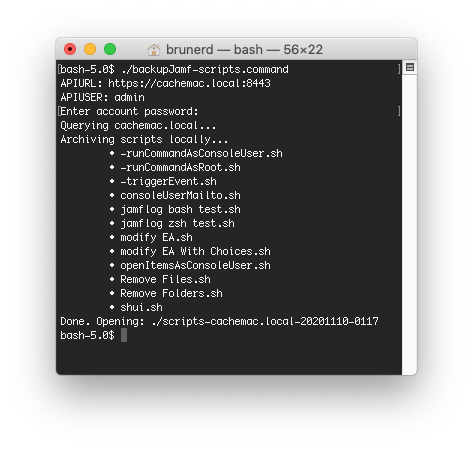
</plist>As you can see things are a bit more complicated now. Applications & Custom Settings won’t make payloads like this and if you upload this to Jamf, make sure to sign it (with something like Hancock) otherwise it will throw out the stuff it doesn’t understand. Just look at what it does understand out of all that.
And if you wonder, “Well doesn’t the Jamf GUI let you build a config profile with the settings you need” the answer is no, it doesn’t, the time is a drop down that goes from “Immediately” to “8 hours” just a hair shy of 2147483647
No, I haven’t made a “Jamf idea” about this, although I did make an unfruitful FB (FB13736030) with Apple July 2024. I just don’t think they care much about MCX payloads acting weird. Why it needed to so radically change things isn’t clear but for now, if you want something that works, copy the above XML into a file that ends in .mobileconfig, sign with Hancock (or similar) and upload into your Jamf’s Configuration Profiles and scope only to Sonama and higher Macs. Make sure to exclude your old payload from them too. Now, next time your Zoom Room Mac gets an OS update, it will auto-login (if you’ve set that) after restart without getting stuck at the lock screen.